In today’s digital age, cybersecurity has become a critical concern for businesses of all sizes. With the rapid increase in cyber threats, organizations face unprecedented risks to their sensitive data and operations. One effective way to counter these threats is by leveraging managed cybersecurity services. These services provide specialized expertise and technology to detect, prevent, and respond to cyber incidents efficiently. In this article, we will explore how managed cybersecurity services improve threat detection and response, helping businesses maintain robust security and operational resilience.
Understanding Managed Cybersecurity Services
Managed cybersecurity services involve outsourcing an organization’s cybersecurity needs to expert service providers. These providers monitor, manage, and protect IT infrastructure around the clock. Unlike traditional security solutions that rely heavily on internal IT teams, managed services offer advanced tools, continuous monitoring, and proactive threat detection, ensuring that vulnerabilities are addressed before they become critical threats.
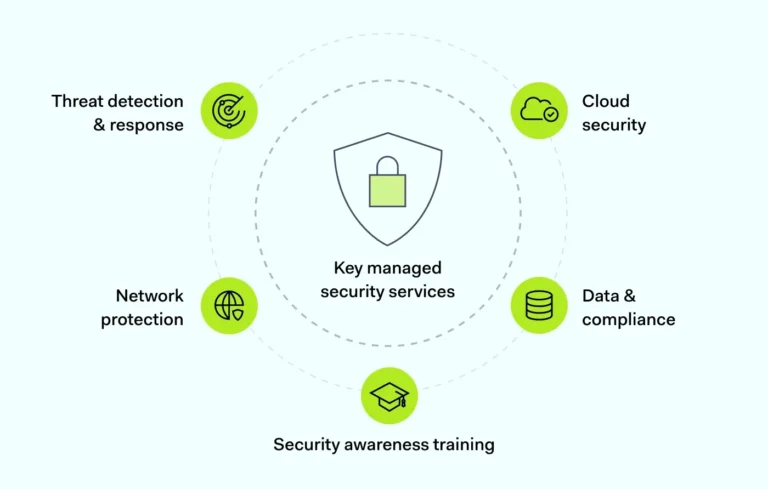
Key components of managed cybersecurity services include:
- Continuous network monitoring
- Threat intelligence and analysis
- Incident response management
- Compliance management
- Security audits and assessments
By incorporating these components, organizations gain access to a holistic cybersecurity framework, enhancing their ability to respond to emerging threats quickly and effectively.
The Growing Need for Advanced Threat Detection
Cyberattacks are becoming increasingly sophisticated. Traditional security measures, such as firewalls and antivirus software, are often insufficient to counter modern threats. Cybercriminals use advanced techniques like ransomware, phishing, and zero-day exploits, which require advanced detection mechanisms.
This is where managed cybersecurity services improve threat detection and response by utilizing advanced tools such as:
- Artificial Intelligence (AI) and Machine Learning (ML): These technologies analyze patterns in network traffic to identify unusual behavior that may indicate a potential attack.
- Security Information and Event Management (SIEM) systems: SIEM platforms collect and correlate data from multiple sources to provide real-time alerts on potential threats.
- Threat Intelligence Platforms: By leveraging global threat data, these platforms enable organizations to anticipate and mitigate cyberattacks proactively.
Such advanced tools allow businesses to identify threats faster, reducing the time attackers have to exploit vulnerabilities.
Proactive Threat Detection Strategies
One of the significant advantages of managed cybersecurity services is the shift from reactive to proactive threat detection. Instead of waiting for an incident to occur, managed service providers continuously scan networks and systems to detect anomalies early.
Proactive strategies include:
- Vulnerability Assessments: Regular scans to identify weaknesses in software, hardware, and network configurations.
- Penetration Testing: Simulated attacks to evaluate the effectiveness of security measures.
- Behavioral Analytics: Monitoring user behavior to detect abnormal activities that may indicate insider threats or compromised accounts.
By employing these strategies, organizations can significantly reduce the risk of breaches and maintain a stronger security posture.
Enhancing Incident Response with Managed Services
Detecting threats is only half the battle; timely and effective response is equally crucial. Managed cybersecurity services improve threat detection and response by offering structured incident response plans and expert intervention.
Key benefits of enhanced incident response include:
- Faster Containment: Immediate action to isolate affected systems and prevent the spread of malware.
- Expert Analysis: Security experts investigate incidents to determine the root cause and implement corrective measures.
- Recovery Support: Managed services assist in restoring systems, recovering lost data, and minimizing downtime.
- Reporting and Compliance: Detailed incident reports help organizations meet regulatory requirements and refine security policies.
This approach ensures that businesses not only detect threats but also respond effectively, minimizing damage and financial losse
Cost Efficiency and Resource Optimization
Many organizations struggle with limited cybersecurity budgets and insufficient in-house expertise. Outsourcing to managed cybersecurity providers allows businesses to access world-class security without the cost of hiring and training specialized staff.
Benefits include:
- Reduced Operational Costs: Managed services eliminate the need for extensive internal security teams and expensive infrastructure.
- Scalable Solutions: Services can be adjusted based on the organization’s size and threat landscape.
- Focus on Core Business: Internal teams can concentrate on strategic projects while experts handle security operations.
By combining cost efficiency with superior threat detection and response capabilities, managed services provide a compelling solution for organizations seeking robust cybersecurity.
Compliance and Regulatory Support
Regulatory requirements in cybersecurity, such as GDPR, HIPAA, and PCI DSS, are complex and ever-changing. Non-compliance can result in heavy fines and reputational damage. Managed cybersecurity services improve threat detection and response by ensuring organizations adhere to these regulations.
Service providers offer:
- Regular compliance audits
- Policy development aligned with industry standards
- Security training for employees
- Documentation and reporting for regulatory reviews
This proactive compliance approach reduces legal risks and builds trust with clients and stakeholders.
Real-World Examples of Effective Managed Cybersecurity
Organizations across industries have successfully leveraged managed cybersecurity services to strengthen their security posture. For instance, financial institutions use continuous monitoring and AI-driven threat detection to protect sensitive customer data. Healthcare providers rely on managed services to secure patient records and maintain HIPAA compliance.
Even small and medium-sized enterprises (SMEs) benefit from outsourced cybersecurity, as it allows them to access enterprise-level protection without the complexity and cost of building in-house capabilities.
Choosing the Right Managed Cybersecurity Provider
Selecting the right provider is critical for maximizing the benefits of managed cybersecurity. Key considerations include:
- Expertise and Certifications: Look for providers with recognized cybersecurity certifications and a proven track record.
- Service Scope: Ensure they offer comprehensive monitoring, threat intelligence, and incident response services.
- 24/7 Support: Cyber threats can occur at any time, making round-the-clock monitoring essential.
- Customized Solutions: Providers should tailor services to match the specific needs and risks of your organization.
A strategic partnership with a capable provider ensures that your business stays ahead of evolving threats.
Future Trends in Managed Cybersecurity
The cybersecurity landscape is continuously evolving. Emerging trends indicate how managed cybersecurity services improve threat detection and response in the future:
- Increased Automation: Automation will help reduce response times and free human analysts for complex tasks.
- Integration of AI and Predictive Analytics: Predictive tools will anticipate attacks before they happen.
- Cloud Security Expansion: As more businesses move to the cloud, managed services will focus on securing hybrid and multi-cloud environments.
- IoT Protection: With the growth of connected devices, managed services will provide specialized threat detection for IoT networks.
Staying informed about these trends allows organizations to adapt and maintain resilient cybersecurity defenses.
Conclusion
In an era of escalating cyber threats, relying solely on internal IT resources is no longer sufficient. Managed cybersecurity services improve threat detection and response by providing advanced monitoring, proactive detection strategies, rapid incident response, and regulatory compliance support. By partnering with a reliable managed service provider, organizations can safeguard their data, reduce operational risks, and focus on their core business objectives. Investing in managed cybersecurity is not just a technical decision—it’s a strategic move to ensure long-term business resilience in the digital age.